Full IT Outsourcing
Full IT Outsourcing
With BA Tech’s model, we oversee the execution of IT operations while the client retains full control over their IT strategic functions, enabling them to focus on aligning IT strategies with their organization’s business objectives.
BA Tech helps transform IT into an optimal, highly effective and reliable resource while keeping costs as low as possible. IT operations require major investments in technology, systems, infrastructures and management tools on an ongoing basis. To obtain optimal performance, IT operations must be executed based on a factory-type delivery model that requires critical mass and the recurring use of best practices. That’s what sets BA Tech’s full IT outsourcing apart—we have perfected this delivery model from decades of experience.
Proof of Concept
Through a preliminary study (proof of concept), BA Tech can demonstrate the feasibility of full IT outsourcing while committing to deliver identified benefits.
EXPERT PERSPECTIVE
Our security engineers are trained to quickly discover & reduce risk
GAIN BUY-IN
Get leadership & IT on the same page for intelligent spending

EFFICIENT COMPLIANCE
Meet necessary requirements for your industry
Cloud Platforms
Amazon Web Services
Microsoft Azure
Salesforce
Google App Engine
Alibaba Cloud
GET IN TOUCH
TOP SECURITY SPENDING DRIVERS
63%
protection of sensitive data
56%
regulatory compliance
31%
reducing incidents & breaches
WHAT WE OFFER
HIPAA RISK ASSESSMENT
Designed specifically for organizations with Health Insurance Portability and Accountability Act (HIPAA) compliance considerations, our HIPAA Risk Assessment (HRA) identifies gaps and security risks within an organization and details how vulnerabilities can result in a breach of Protected Health Information (PHI). View a sample report.
CIS CONTROLS RISK ASSESSMENT
This assessment evaluates your organization’s systems and associated vulnerabilities following the Center for Internet Security (CIS) Controls framework, a prioritized set of best practices for protection developed by cybersecurity experts around the world. With a specific focus on the technical aspects of organizational security, this assessment can provide valuable insight regarding whether your organization’s security tools and appliances are configured correctly and providing the level of security protection you need. View a sample report.
NIST RISK ASSESSMENT
For a more comprehensive look into your organization’s complete risk profile, our NIST Risk Assessment utilizes the National Institute of Standards and Technology (NIST) compliance framework as a guide to evaluate your security posture beyond the technology aspects. Our experts take a closer look at your organization as a whole, including (but not limited to) policies & procedures, documentation, processes, and more to identify security gaps and vulnerabilities. View a sample report.
WHICH PRESENTATION IS RIGHT FOR YOU?
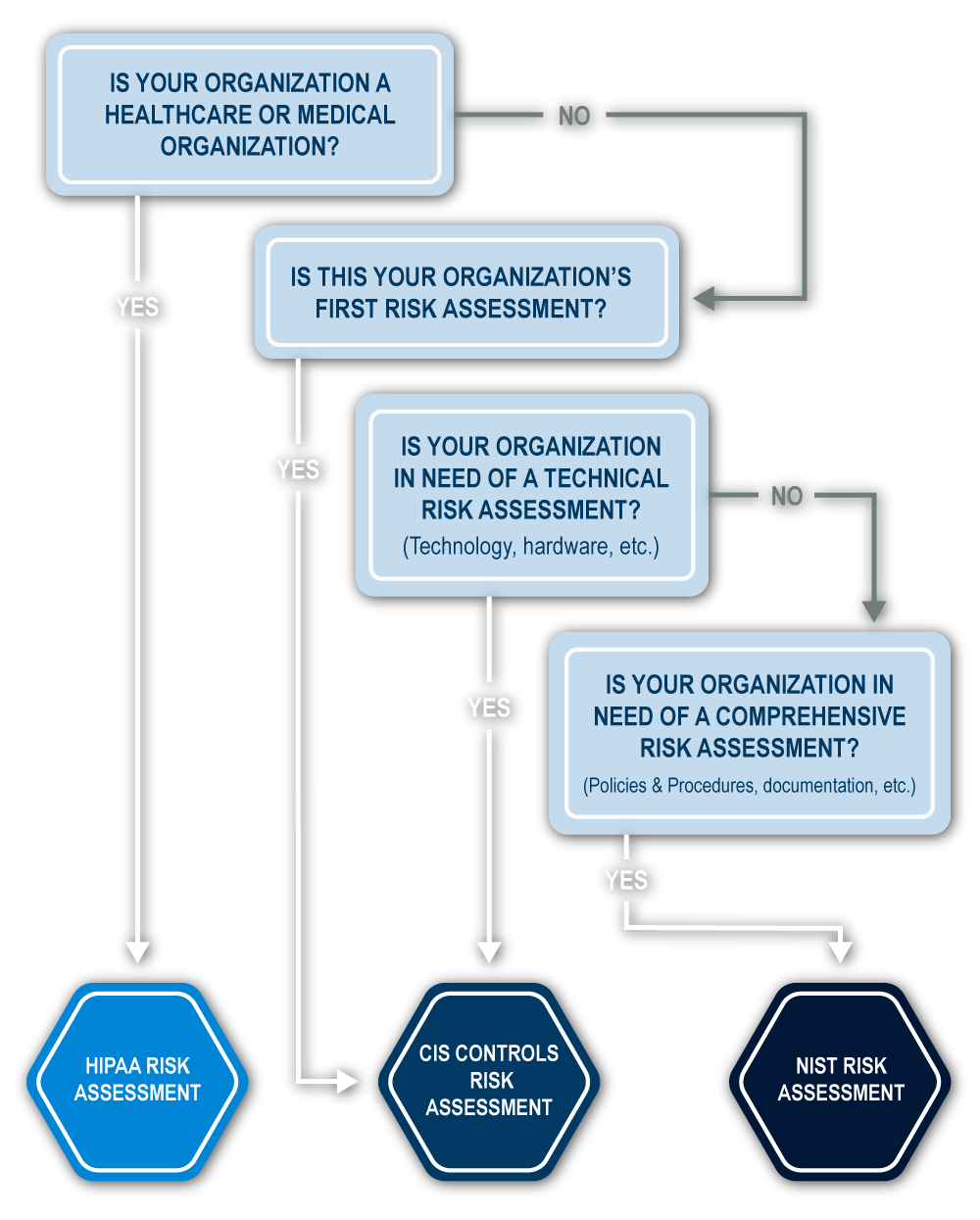
STILL NOT SURE WHICH RISK ASSESSMENT IS RIGHT FOR YOU? TALK TO ONE OF OUR EXPERTS.
OUR RISK ASSESSMENT PROCESS INCLUDES FOUR KEY PHASES:
DATA COLLECTION
Involves a review of existing info & documentation, including existing security policies and procedures & known vulnerabilities

INTERVIEW
Enables our team to understand how your organization currently deals with various aspects of information security controls and management
ANALYSIS
Our team assesses your organization’s vulnerabilities, strengths, and opportunities, then evaluates the results against standard security requirements & benchmarks
REPORTING
A formal report containing an overview of the risks identified & recommended solutions is delivered at the end of the process
BLUEPRINT AND STRATEGY REPORT:
Uses advanced tactics to mimic real world attacks
Provide a detailed look into your organization’s security environment
Pinpoints areas for safeguards and reforms
Outline options that match your budget
Meet compliance mandates
PENETRATION TEST OR RISK ASSESSMENT?


